The world has witnessed the destructive force of Ransomware last year. A new ransomware is spreading quickly across China that has already infected more than 100,000 computers in the last four days and the number is continuously increasing every hour.
The strength thing about the new virus is, it doesn’t demand ransom payments in Bitcoin. This cyber attack only targeting Chinese users.
The attackers are asking the victims to pay 110 yuan (USD 16) in ransom through WeChat Pay. Note that WeChat is China’s most popular messaging app.
It also includes an additional ability to steal users’ account passwords for Alipay, NetEase 163 email service, Baidu Cloud Disk, Jingdong (JD.com), Taobao, Tmall, AliWangWang, and QQ websites.
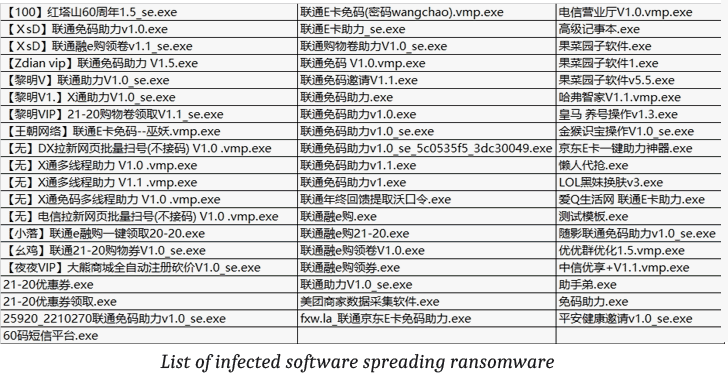
This attack is known as A Supply Chain Attack. According to a Chinese cybersecurity and anti-virus firm Velvet Security, attackers added malicious code into the “EasyLanguage” programming software.It is used by a large number of application developers.
More than 100,000 Chinese users who installed any of the above listed infected applications got their systems compromised.
One pop-up opening and asking users to pay 110 yuan to attackers’ WeChat account within 3 days to receive the decryption key.
If not paid within the time, the malware threatens to delete the main decryption key from its remote command-and-control server automatically.
Besides encrypting user files, the ransomware also silently steals users login credential for popular Chinese websites and social media accounts and send them to a remote server.
It also gathers some system information including screen resolution, CPU model, network information and list of installed software.
Chinese cybersecurity experts found that the ransomware has poorly been programmed and the attackers lied about the encryption process.
Velvet security team has done a good job. It created and released a free ransomware decryption tool that can easily unlock encrypted files for victims. So no need to pay them any ransom.
Researchers also managed to crack and access attackers’ command-and-control and MySQL database servers, and found thousands of stolen credentials stored on them.
Researchers have found a suspect, named “Luo,” who is a software programmer by profession and developed applications like “lsy resource assistant” and “LSY classic alarm v1.1”
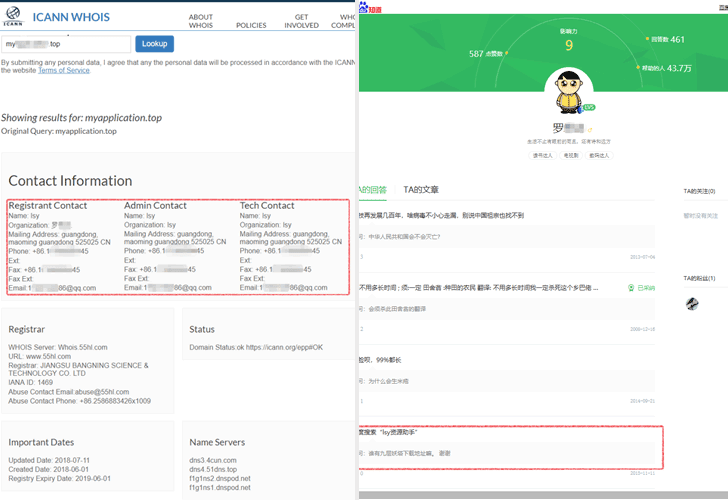
WeChat has also suspended the attackers account from its service that was being used to receive the ransom payments.
Velvet researchers have also informed the Chinese law enforcement agencies with all available evidence for further investigation.